How to Build an AI Prior Authorization Assistant That Prepares PA Requests in Minutes
Thirteen hours per week. That's what the average physician's practice spends on prior authorization, according to the AMA's 2024 Prior Authorization Physician Survey. Across the US medical system, that adds up to roughly $35 billion a year in administrative spend (Sahni et al., Health Affairs Scholar, 2024). 94% of physicians say PA delays patient care. 29% have seen a serious adverse event tied to a PA holdup.
An AI prior authorization assistant is the obvious fix, and the regulatory clock is making it urgent. Under CMS-0057-F, effective January 1, 2026, payers must respond to standard PA requests within 7 calendar days and expedited requests within 72 hours. CMS Director of Medicare Chris Klomp, speaking at the AMA National Advocacy Conference in February 2026, put it plainly: "There should be no human working on prior authorization, period."
The bottleneck has moved. Payers now have to decide faster, so providers have to submit faster and submit clean. This guide is a practical build brief: the data an AI PA assistant needs, the architecture that works, the compliance posture it has to hold, and where to accelerate delivery without cutting corners on HIPAA.
How do you build an AI prior authorization assistant?
Build it around five layers: EHR data access, payer criteria retrieval, AI-assisted evidence matching, request drafting, and human review. The assistant should pull only the relevant clinical data, match it against current payer rules, draft a source-cited PA request, and keep a clinician in control of final submission.
Key Takeaways:
- Prior authorization automation is no longer just an efficiency play. CMS-0057 raises the bar for faster payer responses, which means providers need cleaner, more complete PA submissions from the start.
- The real value of an AI PA assistant is preparation, not decision-making. The tool should check requirements, extract chart evidence, match payer criteria, draft the request, and flag gaps, while a clinician stays in control of review and submission.
- Compliance has to be designed into the workflow, not taped on later. A serious PA automation tool needs BAAs across the vendor chain, audit logging, RBAC, data minimization, source-linked clinical claims, and a human-in-the-loop approval path.
What a Prior Authorization Request Actually Involves
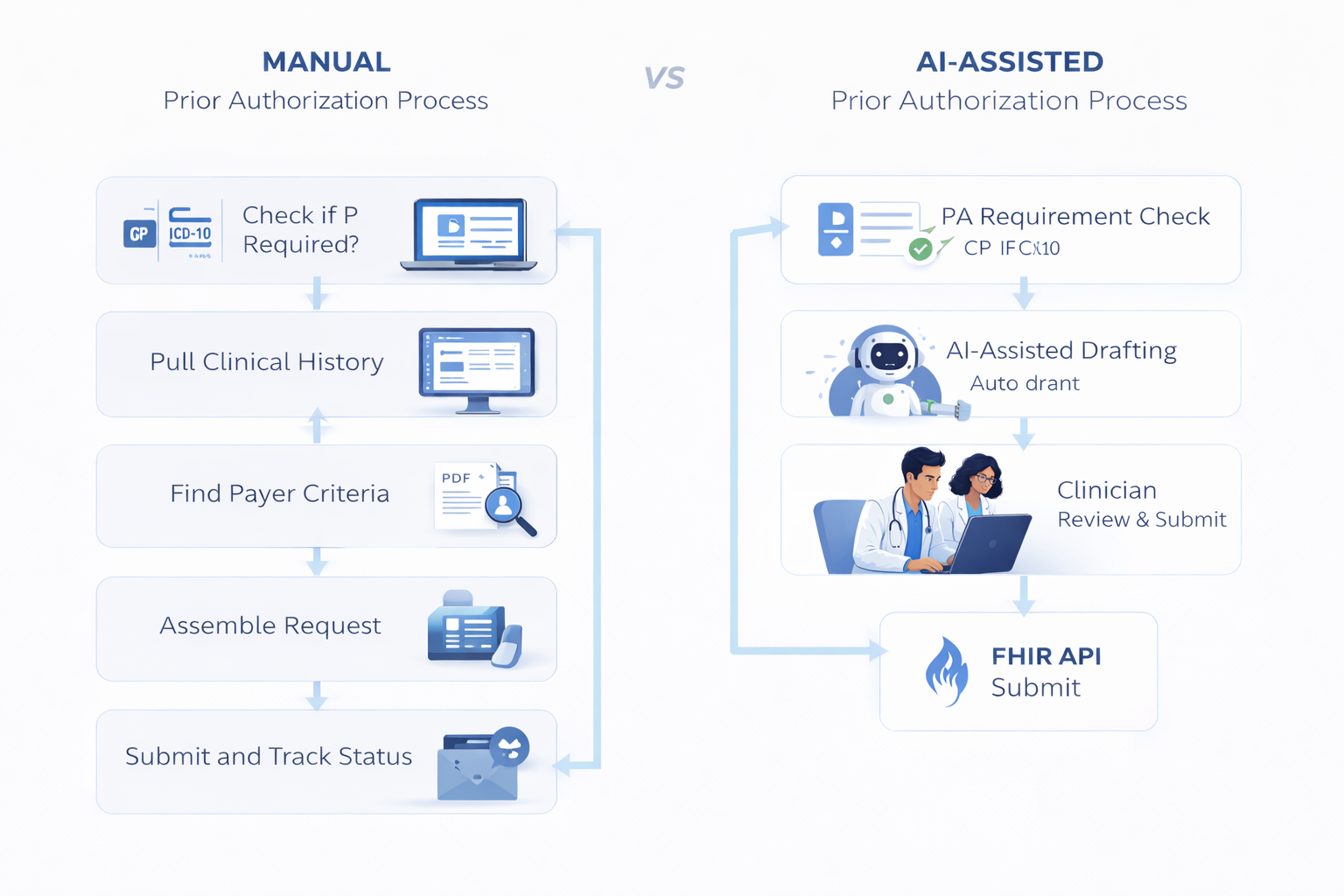
Before walking through an automated version, it helps to see the manual one end to end. For a single request, a staff member typically works through:
- Check if PA is required. Cross-reference the payer, plan, CPT code, and ICD-10 codes against the payer's current requirements. Rules change, so yesterday's answer may not hold today.
- Pull the clinical history. Open the EHR, scan notes, medications, imaging, and labs for what's relevant.
- Find the payer's criteria. Hunt down the specific medical necessity criteria, often a PDF policy buried on the payer's site.
- Assemble the request. Fill in the payer portal, fax form, or X12 278 transaction. Attach supporting documentation.
- Submit and track. Send, then check back for status through a separate portal login or phone call.
- Handle denials. If denied, read the reason, pull more evidence, and prepare an appeal.
Only 35% of medical-industry PAs use electronic prior authorization via X12 278 today (2024 CAQH Index). The rest run on portals, phone, and fax, which is where most patient care delays originate. CAQH estimates full electronic adoption would save the industry $449 million annually and up to 12 minutes per transaction (2022 CAQH Index).
The administrative burden shows up in the numbers: 40% of physicians employ staff who work exclusively on PA, 89% say PA contributes to burnout, and 78% report patients abandoning treatment because of PA barriers (AMA 2024).
A prior authorization workflow that eats this much clinical time isn't sustainable, and the 2026 CMS response windows only raise the stakes for submitting clean the first time. For healthcare providers operating at any scale, prior authorization automation is no longer optional infrastructure — it's the only way to meet the new response windows without adding headcount.
What an AI Prior Authorization Tool Actually Does
Strip away the hype around healthcare AI, and the assistant does four concrete jobs. This is agentic AI in a narrow lane — each job maps to a step that currently eats staff time.
1. PA Requirement Check
Given a CPT code, ICD-10 code, and payer, the tool answers whether PA is required at all. This alone eliminates a meaningful share of unnecessary submissions, where staff prepare requests for procedures that never needed one.
2. Clinical Context Extraction
The tool uses natural language processing to read the patient's chart and pull the data points that matter for this request: prior treatments tried, relevant diagnoses, lab values, imaging results, medication history. What a staff member spends real time finding manually, the assistant surfaces in seconds, with every data point linked back to its source in the EHR.
3. Criteria Matching
The payer has criteria. The patient has history. The tool compares them and flags the case as a strong approval, a gap (missing documentation or an unmet criterion), or a likely denial. Gaps surface early, before the request goes out, so the clinician can gather more evidence or pursue a different path.
4. Request Drafting
The tool assembles a complete submission through end-to-end document automation: the structured payload, a medical necessity narrative with inline citations to the patient record, and supporting documents attached. The draft is ready for a clinician to review and send.
The Human Stays in the Loop
This last point is load-bearing. A well-designed prior auth AI tool prepares; a clinician reviews and submits. CMS is clear that AI can support coverage determinations but cannot make the medical necessity judgment itself. The goal isn't to remove the clinician, it's to remove the administrative work that gets in their way.
That same human-in-the-loop pattern applies across broader clinical workflow automation: AI can prepare, route, summarize, and flag, but the final clinical judgment needs to stay with the responsible human reviewer.
How to Build a Prior Authorization Tool: Technical Architecture
This is where prior authorization software development moves from concept to concrete build spec. Below is the layered architecture that works for most provider-side implementations. The guiding principle: every clinical fact in the output must be traceable to the patient record. No hallucinations, ever.
Data Inputs
The assistant reads from the EHR. Solid prior authorization FHIR integration is the foundation — for most builds, that means FHIR R4 APIs, specifically the Da Vinci Prior Authorization Support (PAS) Implementation Guide, which is the HL7 standard for electronic PA. Required resources typically include Patient, Coverage, Condition (diagnoses), MedicationRequest, Procedure, Observation (labs, vitals), and DocumentReference (clinical documentation). In practice, Epic integration and Cerner integration differ slightly in how they expose certain resources, which affects the write-back layer more than the read layer; athenahealth is common on the ambulatory side. CMS-0057-F makes FHIR-based PA APIs mandatory for payers on January 1, 2027, so building to this spec now avoids a re-architecture in twelve months.
Payer Rules Engine
Payer criteria vary by payer, plan, and procedure, and payer requirements change constantly. Three approaches:
- Structured rules database. Manually encoded criteria per payer. High accuracy, high maintenance burden.
- CDS Hooks + Da Vinci CRD/DTR. Real-time documentation requirements pulled from the payer at order entry. Limited by payer adoption.
- AI-indexed payer policies. Ingest the payer's published policy PDFs into a vector store and retrieve relevant passages at query time. Fastest to cover breadth; needs strong citation discipline.
Production systems usually combine all three: structured rules for the top-volume payers, AI retrieval for the long tail.
AI Layer
A retrieval-augmented generation (RAG) pipeline that takes the patient's structured clinical context plus retrieved payer criteria, and drafts a medical necessity narrative. Two non-negotiables:
- Every clinical claim in the output must cite a source field in the EHR (e.g., Condition/abc-123 or Observation/xyz-456).
- The model does not fabricate values. If a criterion is unmet or data is missing, it flags the gap rather than filling it.
Run the model behind a server you control, never client-side, and use an LLM provider that will sign a BAA.
Form Generation
Output the draft in the target format. For direct electronic submission, that's an X12 278 transaction. For FHIR-native payers, it's a Da Vinci PAS Bundle. For portal-only payers, pre-fill the portal fields through a browser automation layer. Attach supporting documents as FHIR DocumentReference resources.
Status Tracking
After submission, poll the payer's PAS inquiry endpoint (or scrape portal status where no API exists). Surface pending, approved, denied, or additional-info-needed states back to the staff user. Log every status change for audit.
Denial Handling
On denial, parse the reason code (CMS-0057-F requires payers to provide specific denial reasons from January 2026). Pull additional supporting evidence from the record, draft an appeal narrative using the same RAG pattern, and queue it for clinician review.
For teams already investing in telehealth app development, prior authorization is often the next workflow to automate because it sits directly between care delivery, payer rules, and patient access.
Compliance and Security Requirements
The compliance posture required to automate prior authorization with AI sits on four layers. Three are federal or operational: HIPAA, the CMS-0057-F interoperability rule, and the human oversight boundary that keeps AI on the right side of medical necessity. The fourth, state-level AI healthcare laws, is emerging fast and worth watching.
HIPAA: The Vendor Chain Is Your Problem
The assistant touches PHI at every step: patient demographics, diagnoses, medications, payer IDs. Every vendor in the stack that processes that data must be HIPAA compliant and covered by a signed BAA. Miss one, and the whole chain is non-compliant. At minimum, that means BAAs with:
- Your EHR integration layer
- Your LLM provider
- Your vector database
- Your hosting and backend providers
- Your email service
- Your browser automation vendor, if you use one for portal-only payers
Beyond vendor contracts, three controls do most of the work:
- Audit logging on every PHI access, not just submissions: who pulled the chart, what fields they touched, which draft went out.
- Role-based access controls that separate staff who prepare requests from clinicians who submit them.
- Data minimization: pull only the clinical fields this request actually needs, not the whole chart.
CMS-0057-F: A Rule That's Also an Edge
The 7-day response window changes the provider's incentive structure. A clean, complete first submission is now worth more, because a rejected one burns days you don't get back.
Specific denial reasons, mandatory from January 2026, mean your appeal workflow can be programmatic rather than guesswork. Build to the Da Vinci PAS IG now and you're ahead of the January 2027 FHIR API mandate instead of scrambling to retrofit.
State AI Laws: The Payer Side Goes First, Providers Are Next
California's SB 1120, the Physicians Make Decisions Act, took effect January 1, 2025. It regulates how health plans can use AI in utilization review and utilization management: AI cannot make the medical necessity determination, decisions must be based on the individual patient's clinical circumstances (not group datasets), and the algorithms must be open to audit. Other states are moving similar bills.
The law targets payers, not providers, but it matters for anyone building a provider-side PA tool. It confirms the human-in-the-loop design pattern is the legal baseline, not a best practice, and a PA assistant that produces clean, auditable drafts with full source traceability is well positioned for whatever variant lands in your state next.
AI as Decision Support, Not Decision-Maker
All of this points at one design principle: the tool prepares, the clinician reviews and submits, and the audit trail shows a human made the call. Any architecture that drifts from this shape is one policy update away from being non-compliant.
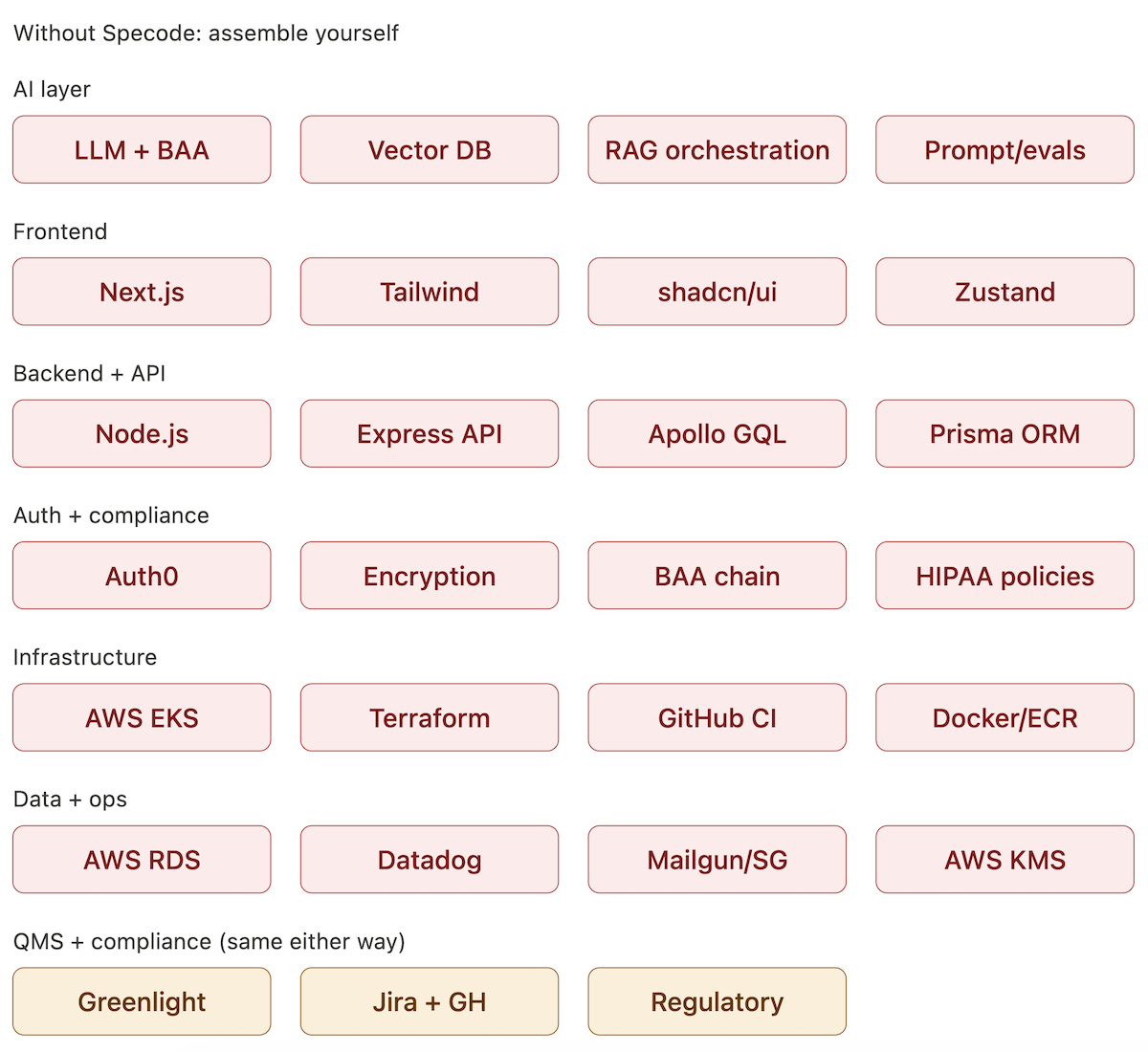
Build, Buy, or Build on Specode
Once you've seen the architecture and the compliance layers, the buy-versus-build question gets concrete. Three paths:
The same build-versus-buy logic shows up in healthcare marketplace development: the hard part is rarely the front-end directory or intake form, but the regulated workflow underneath it.
The decision to build a prior authorization tool from scratch is the right call if you have the engineering team to spec FHIR integrations, negotiate a BAA across every vendor in the chain, and maintain a rules engine that tracks payer policy changes. Most provider-side teams don't have that bench.
Off-the-shelf PA vendors are fast, but they lock you into their payer coverage, their workflow assumptions, and their roadmap. If your clinical workflows are standard and your payer mix is mainstream, that's fine. If either is custom, you'll hit the edges quickly.
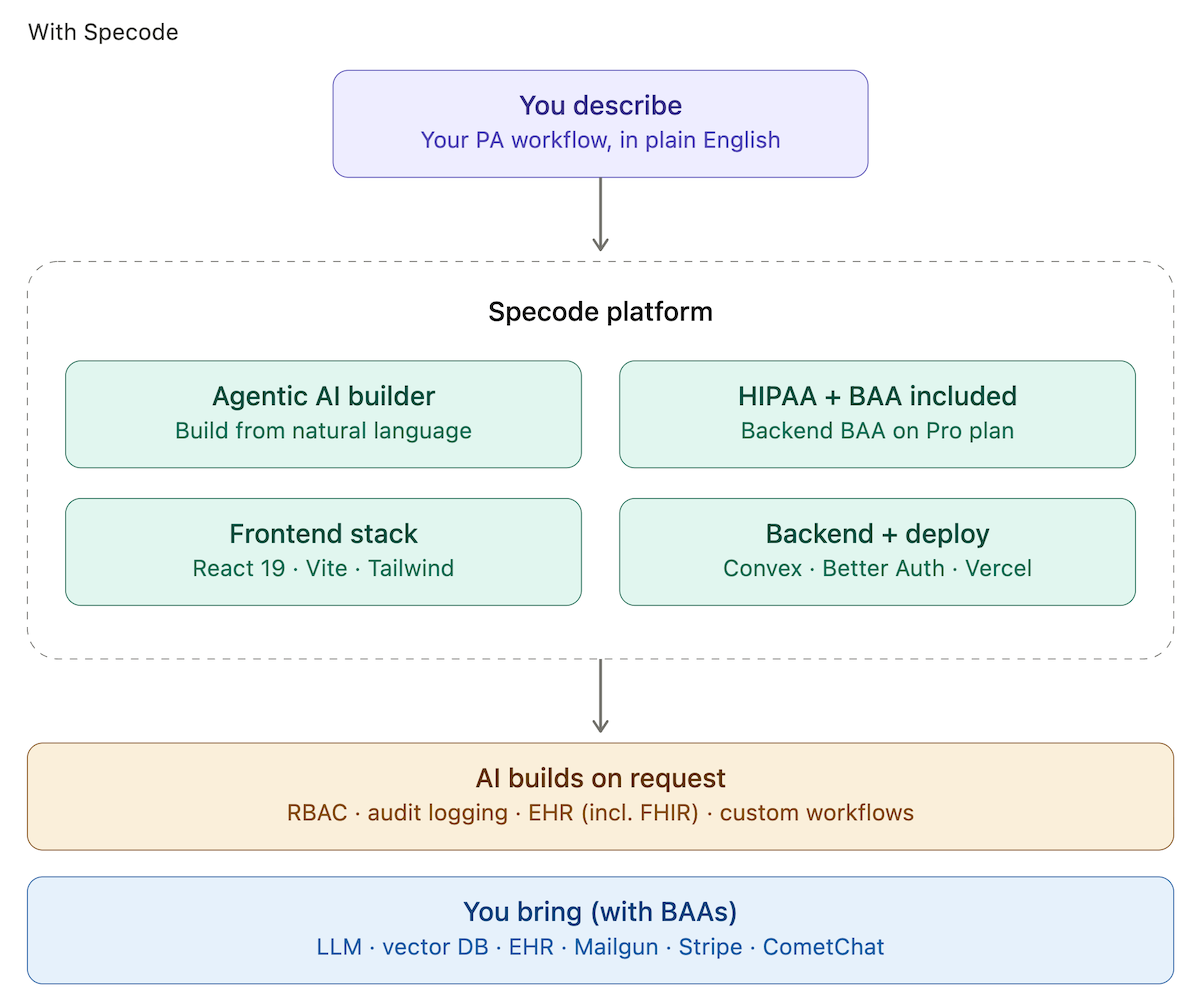
Building on Specode threads the needle: a HIPAA-compliant healthcare app builder with the backend hosting BAA included on the Pro plan, and an AI builder that assembles the PA workflow (including prior authorization EHR integration with Epic, Cerner, or athenahealth) from a plain-language description. The same foundation extends into adjacent systems — revenue cycle management, denial management, patient-facing portals — as your footprint grows. You own the code. If your needs outgrow the platform, you export and keep going.
What a Real PA Assistant Looks Like in Practice
Take a concrete case. A pulmonologist orders a PET scan for a patient with suspected lung cancer. The patient has Aetna commercial coverage. PA is required.
The Manual Path Today
A medical assistant opens the EHR, copies the diagnosis and CPT codes, calls Aetna to confirm PA is required, pulls the payer's current PET imaging criteria, cross-checks the patient's prior imaging and biopsy history, fills in the portal, uploads documents, and submits.
Round trip: about 45 minutes per PA, not counting the clinical workflow disruption every time a clinician has to circle back. Efforts to reduce prior authorization time target exactly this kind of friction. A missing-info kickback starts another cycle.
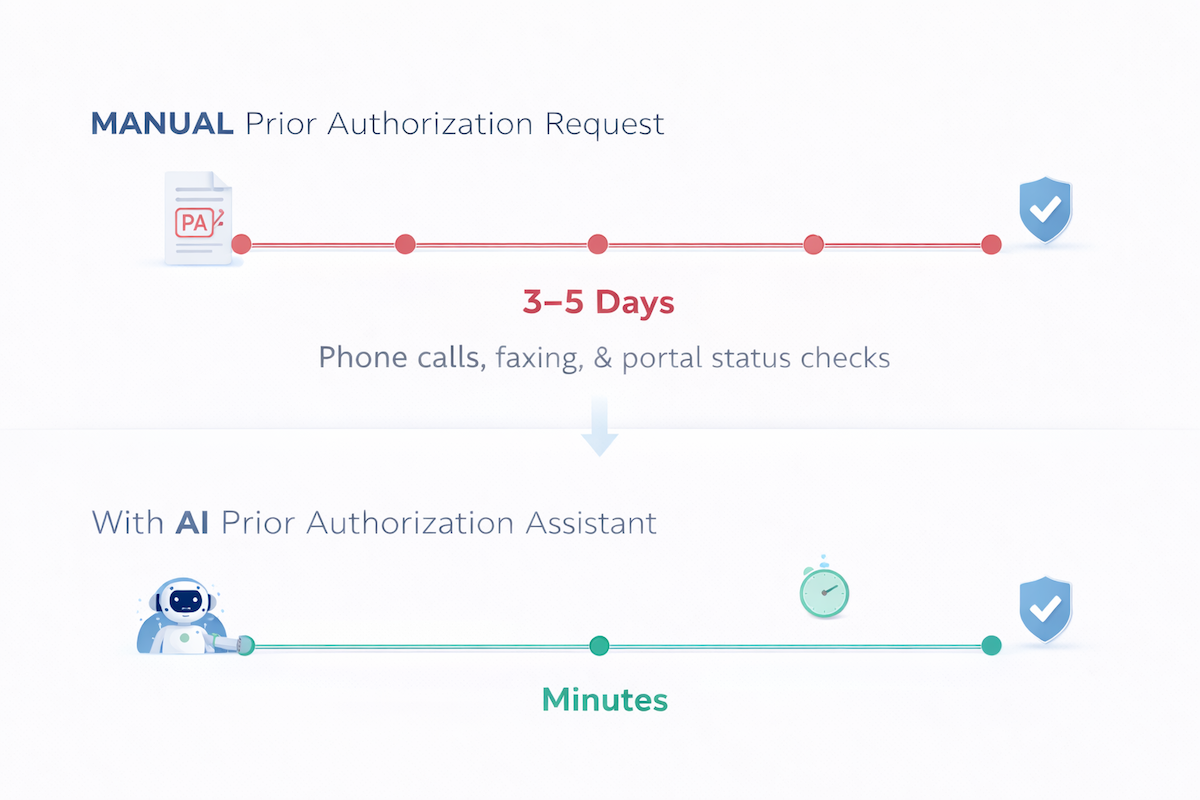
The Assisted Path
At order entry, the tool flags that PA is required for this CPT/payer combination. It pulls the patient's imaging and pathology history, matches it against Aetna's current PET imaging criteria, drafts a medical necessity narrative with inline citations to the chart, and stages a complete submission in the payer's format. The clinician reviews, edits if needed, and submits.
Target elapsed time: about 4 minutes. That's the AI prior authorization tool's real leverage: a clean first-pass submission means no multi-day loop of denials and resubmissions. Because gaps surface before submission rather than after, the prior authorization denial rate drops and the first-pass approval rate climbs.
Minutes, not days.
Build Your AI Prior Authorization Assistant on Specode
If the architecture and compliance posture in this guide look right for your team, the question becomes execution. Deciding how to build a prior authorization app that actually fits your workflows is less about the AI itself and more about the scaffolding around it — auth, audit, BAAs, EHR reads, portal write-backs. Specode compresses PA request automation into a healthcare automation foundation anyone on your team can drive.
You describe the PA workflow you want in plain English: which payers, which CPT categories, what the reviewer screen looks like, which EHR you're reading from. The AI builder assembles the application on a HIPAA-ready foundation, with the backend hosting BAA included on the Pro plan. When you need RBAC, audit logging, FHIR integrations, or denial-appeal flows, you describe them and the AI builds them.
A built-in HIPAA Compliance Agent scans the generated code for common violations before you ship. You own the source, so if your needs outgrow the platform you export and keep going.
With prior authorization reform accelerating at the federal level and payer response windows tightening in 2026, the window to be ready is short. Most teams go from blank project to a testable PA assistant in 2 to 6 weeks: describe your PA workflow in the Specode AI builder and see what ships this week. Pro starts at $1,000/month with no long-term contract.
See how your AI prior authorization tool could take shape on Specode — compare plans and get started.
Frequently asked questions
An AI prior authorization assistant typically needs patient demographics, coverage details, diagnoses, medications, procedures, labs, vitals, imaging results, and relevant clinical notes. In FHIR terms, that usually means resources like Patient, Coverage, Condition, MedicationRequest, Procedure, Observation, and DocumentReference. The key is data minimization: the tool should pull only the fields needed for that specific PA request, not the entire chart.
A production-grade PA assistant usually combines three methods: structured rules for high-volume payers, real-time payer requirements where Da Vinci CRD/DTR support exists, and AI-indexed payer policy documents for the long tail. The safest design retrieves the current policy language at request time and cites the exact source used, instead of relying on stale hardcoded rules.
No. An AI prior authorization assistant should prepare the request, extract supporting evidence, flag documentation gaps, and draft the medical necessity narrative. A clinician or authorized human reviewer should still review and submit the request. AI can support the workflow, but the medical necessity judgment cannot be delegated to the model.
HIPAA compliance is the baseline, which means signed BAAs with every vendor that touches PHI: hosting, backend, LLM provider, vector database, EHR integration layer, email service, and any browser automation vendor. You also need audit logging, role-based access controls, data minimization, and a clear human-in-the-loop workflow. Depending on your market, SOC 2, HITRUST, or payer/vendor security reviews may also come into play.
Most teams can get from a blank project to a testable PA assistant in about 2 to 6 weeks, depending on payer coverage, EHR integration complexity, review workflow, and submission channels. A narrower first version, for example one specialty, one EHR, and a few high-volume CPT categories, is the fastest path. Trying to automate every payer and every edge case on day one is how good projects go to die in a spreadsheet.
CMS-0057 shortens payer response windows to 7 calendar days for standard PA requests and 72 hours for expedited requests starting January 1, 2026. That makes clean first-pass submissions more valuable because missing information can burn time quickly. Providers should build workflows that prepare complete requests, capture denial reasons, support appeals, and move toward FHIR-based PA submission ahead of the January 2027 API mandate.









